More and more organizations is taking advantage of using MFA for their users and there is no reason for them not to since it`s free for all Office 365 users and also for all Azure AD users if you are not using the Office 365 services. But after you enable it for your users, are you sure everyone is enabled?
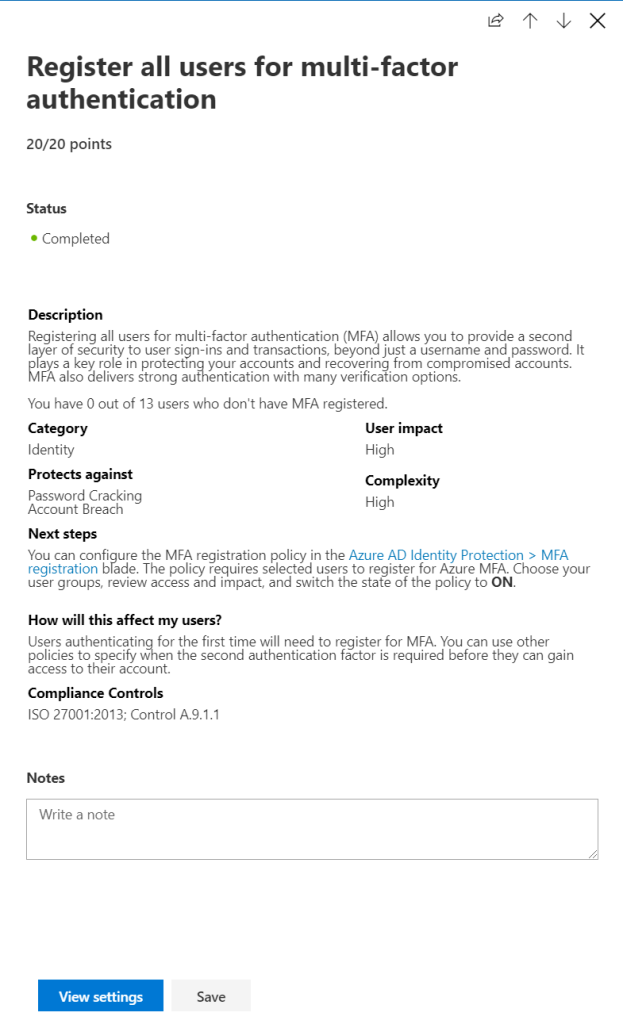
You may have seen at the Secure Score that not all users are registred for MFA, and if you do so you have users with no MFA! So these users may be victims for bruteforce attacks so it`s super important to remediate all users to see how everything is configured! Some of the users with no MFA maybe legit and should not have it.
So let`s dig into the materials for a second or two.
First thing is that there is a “Secure Score” check for MFA registered users that will show you how many of your users which are not registered (if any)
If you have any users in that list it would not show who the users are so we need to go deeper in the material to retreive this status.
So to get the list of users who don`t have setup MFA you need to run this PowerShell command with the AzureAD PowerShell module loaded.
Connect-MsolService
Get-MSOLUser -all | where {$_.StrongAuthenticationMethods.methodtype -eq $null} | Select Displayname,UserPrincipalName,BlockCredential,LastPasswordChangeTimestamp,UserType |Out-GridViewAnd now that we have found all users we can check them out why they don`t use MFA and make sure that they use it 🙂
Further on we can check what method users are using when authenticating with MFA. For this I use this script located in Technet PowerShell archives HERE
If you have deployed MFA the Conditional Access way (recommended) you will see that the MFA status on all user are set to “Disabled” but the method is set to what the user are using.
Have checking status on your users! 🙂




