
Entra ID – Authentication methods
First, a little background information of what I`m doing here. Starting from September 30th, 2025 (and as you...

Entra ID PIM – Discovery & Insights
Are you curious about how Entra ID roles are utilized? Or perhaps you’re wondering if any users or...

How Microsoft Entra ID Governance Helps You Manage Your Guest Accounts
If you are like me, you have probably invited many guest accounts to your Microsoft 365 environment over...

Just-enough access strategy
Oversharing is a common challenge in Microsoft 365, as it can expose sensitive data and resources to unauthorized...
Microsoft Graph and Unified search
When we adopt Microsoft 365 Copilot we want all our data to be available for Copilot to use...

Sensitive data? – Label it!
Table of Contents What and Why? How? Wrap up What and Why? Sensitivity labels is part of Microsoft...

Don’t lose your data!
Introduction What do we need to get started with DLP? Wrap-up Introduction I think every organization want to...

Zero trust!
AI can magnify what an organization can do, so making sure that employees, devices, and data stay secure...
Safeguard your data
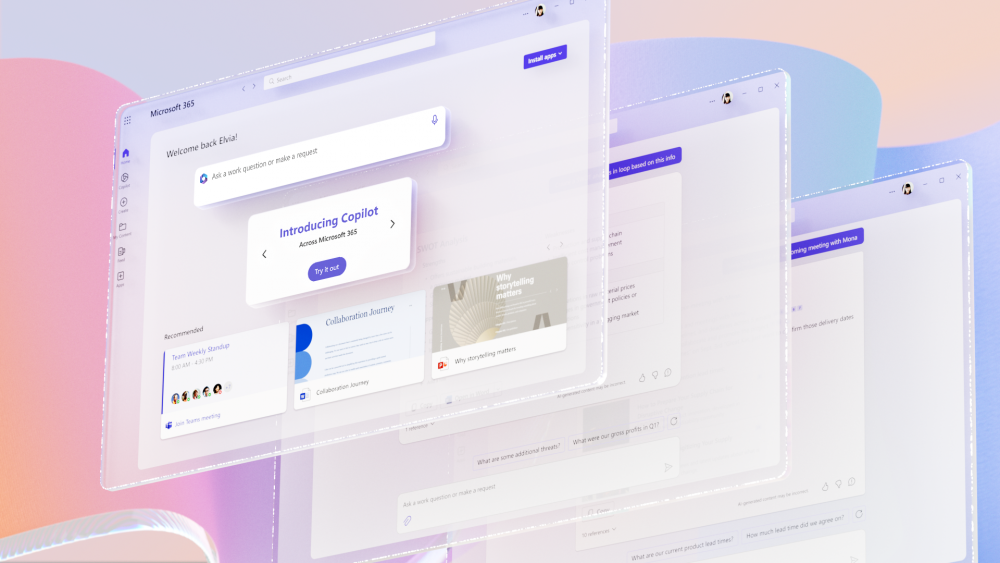
Copilot is coming! But are you ready? Before we can adopt Microsoft 365 Copilot we need to make...
