
Monitor sensitive accounts
Pre-requisites Query Action Group Alert Conclusion and result Pre-requisites A pre-requisites for monitoring sensitive accounts in Azure AD...

What is Microsoft Endpoint Manager?
Many people wonder what Microsoft Endpoint Manager is and how to quickly gain value to their company by...

S for Security in EMS – Microsoft Intune
So this is the third post in my blog post series “S for Security in EMS” and I...
S for Security in EMS – Azure Information Protection
Even tho Azure Information Protection is included within the EMS package i would recomend using the Office 365...
Change to Opt-In in MyAnalytics
Since MyAnalytics is an “Opt-Out” feature in Office 365, some companies wants to change this behavour for their...

S for Security in EMS
Since Enterprise Mobility + Security (EMS) is a core component of Microsoft 365 services you need to understand...
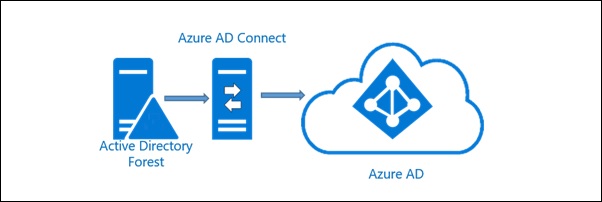
Azure AD Connect sync issues
Now and then we get errors in our Azure AD Connect syncronization, or that said – my customers...

How do I know all my users are enabled for and using MFA?
More and more organizations is taking advantage of using MFA for their users and there is no reason...

Ignite – some of the news I got first day
So! Day one at Ignite is over and what a day! A lot of new features, services and...
